Domain name: cablenetlinks.com
Registry Domain ID: 2480805009_DOMAIN_COM-VRSN
Registrar WHOIS Server: whois.namecheap.com
Registrar URL: http://www.namecheap.com
Registrar: NAMECHEAP INC
Name Server: dns1.namecheaphosting.com
Name Server: dns2.namecheaphosting.com
DNSSEC: unsigned
Subdomains:
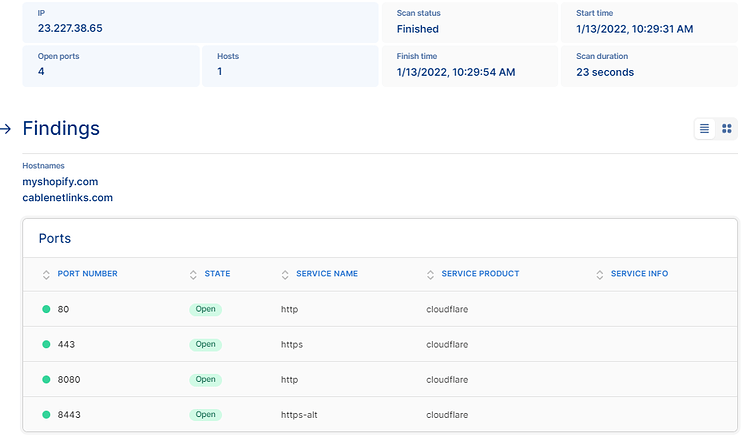
cablenetlinks.com,23.227.38.65
oldweb.cablenetlinks.com,198.54.120.162
mail.cablenetlinks.com,198.54.120.162
www.oldweb.cablenetlinks.com,198.54.120.162
www.oldback.cablenetlinks.com,198.54.120.162
oldback.cablenetlinks.com,198.54.120.162
Complete subdomain list:
oldweb.cablenetlinks.com
www.cablenetlinks.com
cpcontacts.oldback.cablenetlinks.com
cpcalendars.oldback.cablenetlinks.com
cpanel.cablenetlinks.com
www.oldweb.cablenetlinks.com
oldback.cablenetlinks.com
whm.cablenetlinks.com
webdisk.cablenetlinks.com
cpcontacts.cablenetlinks.com
whm.oldback.cablenetlinks.com
cpcalendars.oldweb.cablenetlinks.com
autoconfig.oldback.cablenetlinks.com
cpcalendars.cablenetlinks.com
autoconfig.cablenetlinks.com
whm.oldweb.cablenetlinks.com
cpanel.oldback.cablenetlinks.com
mail.cablenetlinks.com
ftp.cablenetlinks.com
cablenetlinks.com
autodiscover.cablenetlinks.com
autoconfig.oldweb.cablenetlinks.com
webmail.cablenetlinks.com
cpcontacts.oldweb.cablenetlinks.com
webdisk.oldback.cablenetlinks.com
Portscsan:
https://cablenetlinks.com/robots.txt```
//robots.txt file - contains a fair amount```
| CVE | Summary | Affected Software
| [+] CVE-2018-16487 | A prototype pollution vulnerability was found in lodash| Lodash 4.5.1 |
| [+] CVE-2021-23337 | Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function. | Lodash 4.5.1 |
| [+] CVE-2019-10744 | Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload. | Lodash 4.5.1 |
| [+] CVE-2020-8203 | Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20. | Lodash 4.5.1 |
| [+] CVE-2020-28500 | Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions. | Lodash 4.5.1 |
| [+] CVE-2015-9251 | jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed. | jQuery 1.10.2 |
| [+] CVE-2019-11358 | jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype. | jQuery 1.10.2 |
| [+] CVE-2020-11022 | In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0. | jQuery 1.10.2 |
| [+] CVE-2020-11023 | In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0. | jQuery 1.10.2 |
Anyway, if I find more, I’ll hit this thread up <3